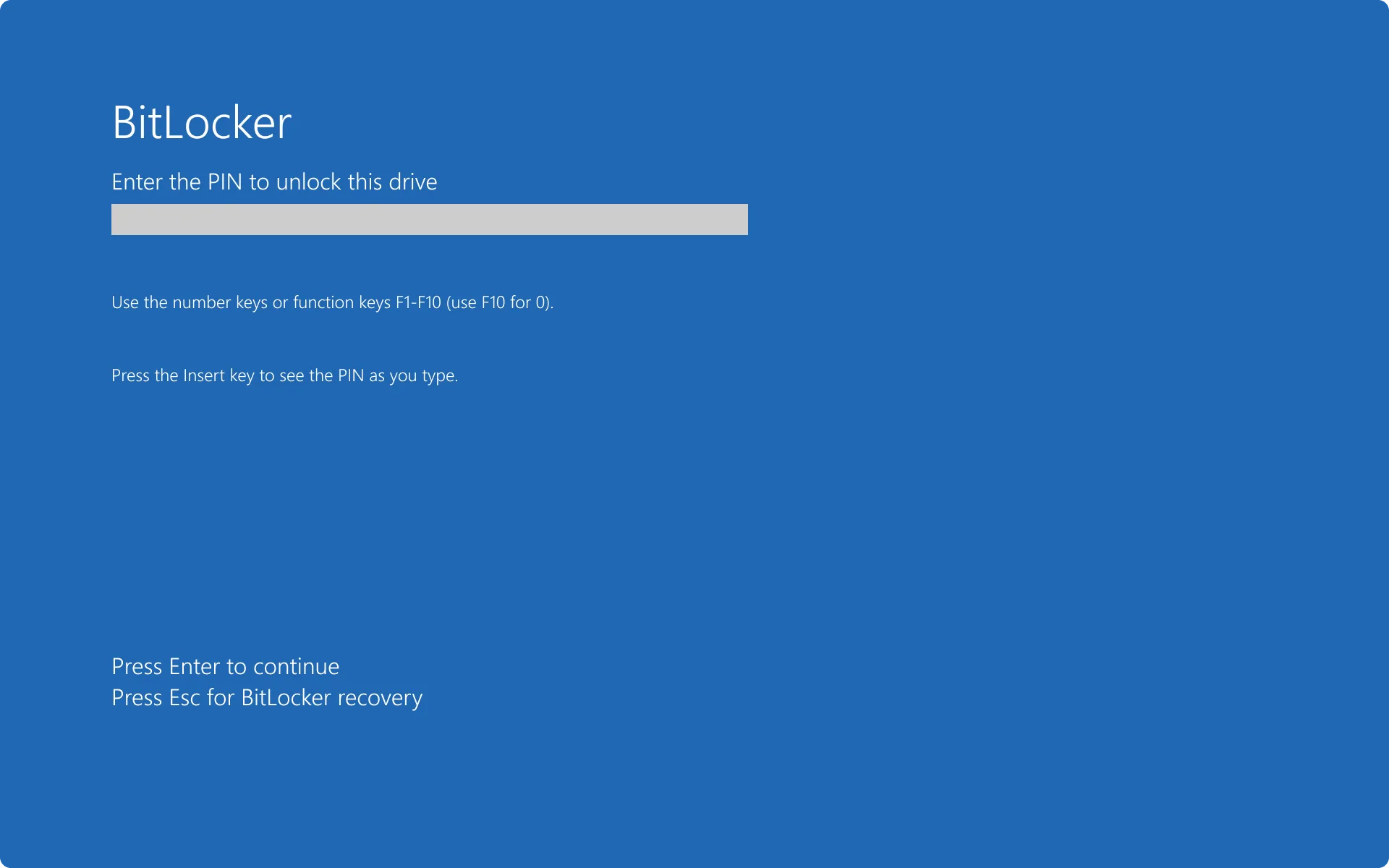
In the ever-evolving field of digital security, the promise of strong encryption offers solace against prying eyes, a bulwark for our most sensitive data. Yet, a recent revelation concerning Microsoft and its ubiquitous BitLocker full-disk encryption system has sent ripples through the tech community, prompting a critical re-evaluation of how much trust we place in default security settings. What began with a single, publicly acknowledged instance in early 2025 has unmasked a deeper, more frequent practice that places Microsoft at odds with privacy advocates and, seemingly, with its industry peers. We believe this isn't just a technical detail; it's a fundamental question about digital autonomy.
The core issue is clear: While BitLocker safeguards countless Windows PCs, its default key recovery mechanism leaves a backdoor – one that Microsoft, under legal duress, is compelled to open for government agencies, including the FBI. This isn't a vulnerability in the encryption itself, but rather in the storage and accessibility of the very keys that unlock our digital lives.
BitLocker's Faustian Bargain: Convenience vs. Control
Microsoft’s BitLocker is an integral part of the Windows ecosystem, designed to prevent unauthorized access to a drive’s contents. Enabled by default on many modern Windows PCs, including Windows 11, it uses strong encryption algorithms like AES 128-bit and AES 256-bit. For most users, its appeal lies in its tight integration and, most importantly, its convenience for key recovery. We recognize the appeal of "set it and forget it" security, but this convenience, we argue, comes with a significant and often unseen cost.
When users set up their PCs with a Microsoft Account, BitLocker automatically backs up recovery keys to Microsoft's cloud by default. While users have options to store keys locally (e.g., USB drive, file, print), the cloud backup is undeniably the path of least resistance. This default setting, Microsoft spokesperson Charles Chamberlayne openly admitted, "carries a risk of unwanted access". We contend that offering a default that "carries a risk of unwanted access" is precisely the kind of security posture that should raise alarms.
And that risk has materialized, not just hypothetically, but in hundreds of actual cases.
The FBI's Quiet Advantage: More Than a One-Off Revelation
The incident that brought this practice into the public eye was widely reported in late January 2026, revealing that Microsoft had provided BitLocker recovery keys for three laptops to the FBI, an action tied to a 2025 court document. This marked the first publicly recorded instance of Microsoft complying with such a request.
However, the notion that this was an isolated event quickly dissolved. Microsoft confirmed it regularly provides BitLocker recovery keys to government agencies when presented with a valid legal order. In the latter half of 2023 alone, Microsoft turned over customer BitLocker encryption recovery keys to U.S. law enforcement 703 times. The company complied with an astonishing 96% of the 730 legal demands it received for BitLocker keys and/or customer data from OneDrive during that period. These disclosures are in response to warrants based on a probable cause standard and are considered legally required under the U.S. Stored Communications Act (SCA). These aren't just numbers; they represent 703 instances where private data, assumed secure by many, was unlocked by a third party.
Without Microsoft's intervention, the FBI and other agencies would largely be stymied. As an ICE Homeland Security Investigations forensic expert stated in a 2025 court document, his agency "did not possess the forensic tools to break into devices encrypted with Microsoft BitLocker, or any other style of encryption". BitLocker's underlying encryption is solid; the vulnerability lies not in the encryption itself, but in Microsoft's default handling of the recovery keys.
The Unencrypted Keys: A Cloud-Based Privacy Lapse
One of the most concerning aspects, as highlighted by cryptography expert Matthew Green and Windows Central, is the suggestion that BitLocker keys uploaded to Microsoft's cloud are reportedly available in an unencrypted state. This means Microsoft itself can access them, making them readily available when a legal order arrives. Windows Central called this a "privacy nightmare" for customers, a sentiment echoed by American Civil Liberties Union (ACLU) counsel Jennifer Granick, who warned that "Remote storage of decryption keys can be quite dangerous."
While Microsoft maintains it does not provide governments with its own encryption keys or the ability to break its encryption, the fact that customer keys are held in a state accessible to the company means the distinction is, for practical purposes, blurred. We find it difficult to reconcile Microsoft's claim of empowering users to decide how to manage keys when the default — and easiest — option leads directly to this level of accessibility for a third party. Critics also point out that a centralized cloud system storing a multitude of recovery keys creates an attractive target for hackers.
Microsoft: An Industry Outlier in Key Management?
Microsoft's approach to key management and government requests stands in sharp contrast to some of its major industry counterparts.
- Apple: Famously resisted an FBI request to unlock an iPhone in 2016, forcing the agency to seek a third-party contractor. More recently, Apple introduced Advanced Data Protection for iCloud, utilizing end-to-end encryption (E2EE) for most user data, which, when enabled, rendered the keys technically inaccessible to Apple. However, the service was later withdrawn for new users in some regions, such as Britain, in February 2025. Its official documentation explicitly states that with this feature enabled, "Apple does not have the encryption keys needed to help you recover" data. Apple offers similar encryption systems (such as FileVault) and provides secure options for key storage, so users can store backup keys online in an encrypted file, generally making them inaccessible to the company without the user's specific key.
- Meta: Similarly, Meta keeps encrypted backups of WhatsApp data, and like Apple, is not known to have provided encryption keys to law enforcement. Some reports indicate Meta stores keys in the cloud using zero-knowledge architectures, meaning only the user can access them.
Johns Hopkins professor and cryptography expert Matthew Green pointedly stated, "Microsoft's inability to secure critical customer keys is starting to make it an outlier from the rest of the industry." We agree. When competitors like Apple and Meta have demonstrably engineered systems where they cannot access user keys even when stored in the cloud, Microsoft's default approach appears to be a deliberate, or at least highly convenient, architectural choice that prioritizes recovery for them over absolute user privacy.
Broader Implications: The 'Digital Life' at Risk
The implications of Microsoft's compliance extend far beyond individual cases. Senator Ron Wyden minced no words, calling it "simply irresponsible for tech companies to ship products in a way that allows them to secretly turn over users' encryption keys". He warned that providing agencies with encryption keys gives them "access to the entirety of that person’s digital life, and risks the personal safety and security of users and their families."
Other critical concerns we see include:
- Scope of Access: Granick noted that providing keys grants access to "information well beyond the time frame of most crimes, everything on the hard drive," requiring trust that agents only look for information relevant to the authorized investigation.
- Foreign Government Demands: The precedent set in the U.S. could easily extend globally. Granick expressed concern that foreign governments with questionable human rights records may also demand data from tech giants like Microsoft, creating a perilous global precedent.
- Increased Demands: Cryptography expert Matt Green believes that now that the FBI and other agencies know Microsoft will comply, they will likely make more demands for encryption keys, expanding this practice.
- Security Risks: Green also raised the potential scenario of malicious hackers compromising Microsoft’s cloud infrastructure and accessing recovery keys, even if physical access to hard drives would still be needed.
True Data Sovereignty: An Active Choice, Not a Default
This situation highlights a fundamental tension between convenience, security, and privacy. While BitLocker's key recovery offers undeniable ease for the average user who might otherwise lose access to their data, it simultaneously creates a centralized point of vulnerability subject to legal demands.
"True data sovereignty requires active management," warns one expert. Default settings offered by technology giants like Microsoft are designed for a balance of security, usability, and legal compliance – not absolute privacy. For users genuinely seeking to protect their digital lives from all forms of unwanted access, including government surveillance, the lesson is clear: relying on default cloud storage for encryption keys is a gamble. Understanding how and where your encryption keys are stored is no longer merely a technical detail; it is a critical aspect of personal security and digital autonomy in the modern age. We urge users to actively take control of their encryption key management rather than blindly trusting the path of least resistance. For enterprises, redirecting keys to on-premises Active Directory or a controlled enterprise key vault is a safer configuration than default cloud backup.








Comments